Disk events anomaly detection API - POST an event
Creates a new disk event rule.
The request consumes and produces an application/json payload.
This request is an early adopter release and may be changed in non compatible way.
| POST |
|
Parameters
| Parameter | Type | Description | In | Required |
|---|---|---|---|---|
| body | DiskEventAnomalyDetectionConfig |
JSON body of the request. Contains parameters of the new disk event rule. |
body | optional |
The DiskEventAnomalyDetectionConfig object
| Element | Type | Description | Required |
|---|---|---|---|
| metadata | ConfigurationMetadata |
Metadata useful for debugging. |
optional |
| id | string |
The ID of the disk event rule. |
optional |
| name | string |
The name of the disk event rule. |
required |
| enabled | boolean |
Disk event rule enabled/disabled. |
required |
| metric | string |
The metric to monitor. The metric element can hold these values. |
required |
| threshold | number |
The threshold to trigger disk event.
|
required |
| samples | integer |
The number of samples to evaluate. |
required |
| violatingSamples | integer |
The number of samples that must violate the threshold to trigger an event. Must not exceed the number of evaluated samples. |
required |
| diskNameFilter | DiskNameFilter |
Narrows the rule usage down to disks, matching the specified criteria. |
optional |
| tagFilters | TagFilter[] |
Narrows the rule usage down to the hosts matching the specified tags. |
optional |
The TagFilter object
A tag-based filter of monitored entities.
| Element | Type | Description | Required |
|---|---|---|---|
| context | string |
The origin of the tag, such as AWS or Cloud Foundry. Custom tags use the |
required |
| key | string |
The key of the tag. Custom tags have the tag value here. |
required |
| value | string |
The value of the tag. Not applicable to custom tags. |
optional |
The DiskNameFilter object
Narrows the rule usage down to disks, matching the specified criteria.
| Element | Type | Description | Required |
|---|---|---|---|
| operator | string |
Comparison operator. The operator element can hold these values. |
required |
| value | string |
Value to compare to. |
required |
The ConfigurationMetadata object
Metadata useful for debugging
| Element | Type | Description | Required |
|---|---|---|---|
| configurationVersions | integer[] |
A Sorted list of the version numbers of the configuration. |
optional |
| clusterVersion | string |
DESK server version. |
optional |
This is a model of the request body, showing the possible elements. It has to be adjusted for usage in an actual request. See the Example expandable section for working sample request.
{
"metadata": {
"configurationVersions": [
"integer"
],
"clusterVersion": "string"
},
"id": "string",
"name": "string",
"enabled": true,
"metric": "LOW_DISK_SPACE",
"threshold": "number",
"samples": 10,
"violatingSamples": 8,
"diskNameFilter": {
"operator": "CONTAINS",
"value": "string"
},
"tagFilters": [
{
"context": "AWS",
"key": "string",
"value": "string"
}
]
}
Possible values
Possible values for the context element in the TagFilter object:
- AWS
- AWS_GENERIC
- AZURE
- CLOUD_FOUNDRY
- CONTEXTLESS
- ENVIRONMENT
- GOOGLE_CLOUD
- KUBERNETES
Possible values for the operator element in the DiskNameFilter object:
- CONTAINS
- DOES_NOT_CONTAIN
- DOES_NOT_EQUAL
- DOES_NOT_START_WITH
- EQUALS
- STARTS_WITH
Possible values for the metric element in the DiskEventAnomalyDetectionConfig object:
- LOW_DISK_SPACE
- LOW_INODES
- READ_TIME_EXCEEDING
- WRITE_TIME_EXCEEDING
Response format
The EntityShortRepresentation object
The short representation of a DESK entity.
| Element | Type | Description |
|---|---|---|
| id | string | The ID of the DESK entity. |
| name | string | The name of the DESK entity. |
| description | string | A short description of the DESK entity. |
{}
Validate payload
We recommend that you validate the payload before submitting it with an actual request. A response code of 204 indicates a valid payload.
The request consumes an application/json payload.
This request is an early adopter release and may be changed in non compatible way.
| POST |
|
Response codes
| Code | Description |
|---|---|
| 204 | Validated. The submitted disk event rule is valid. Response doesn't have a body. |
| 400 | Failed. The input is invalid. |
Example
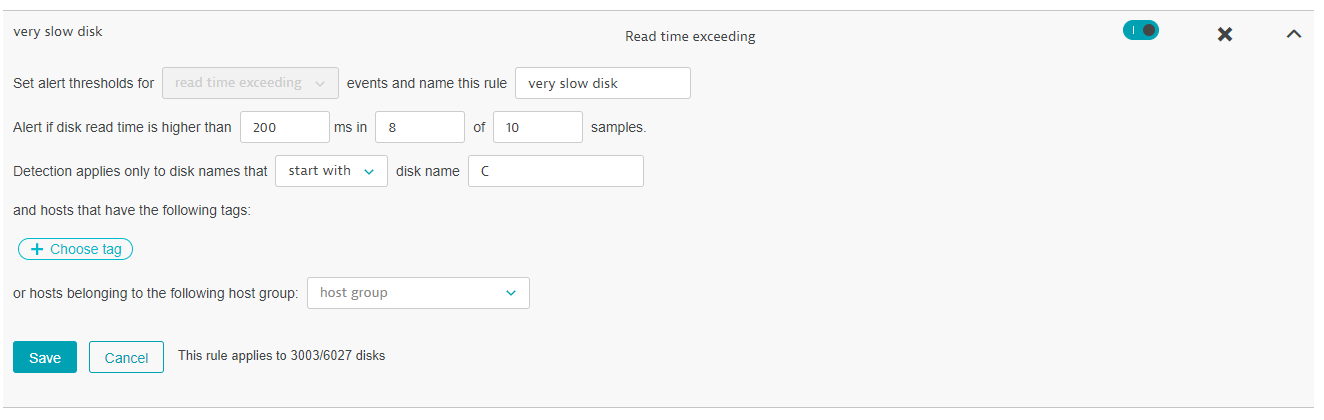
In this example, the request creates a new custom disk event rule named very slow disk. The rule triggers an alert for any disk whose name starts with C and whose read time exceeds 200 milliseconds in 8 out of 10 samples.
The API token is passed in the Authorization header.
You can download or copy the example request body to try it out on your own.
Curl
curl -X POST \
https://mySampleEnv.live.dexp.ae/api/config/v1/anomalyDetection/diskEvents \
-H 'Authorization: Api-token abcdefjhij1234567890' \
-H 'Content-Type: application/json' \
-d '{
"name": "very slow disk",
"enabled": true,
"metric": "READ_TIME_EXCEEDING",
"threshold": 200,
"samples": 10,
"violatingSamples": 8,
"diskNameFilter": {
"operator": "STARTS_WITH",
"value": "C"
},
"tagFilters": []
}
'
Request URL
https://mySampleEnv.live.dexp.ae/api/config/v1/anomalyDetection/diskEvents
Request body
api-examples/config/anomaly-detection/disk-events/post-config.json
{
"name": "very slow disk",
"enabled": true,
"metric": "READ_TIME_EXCEEDING",
"threshold": 200,
"samples": 10,
"violatingSamples": 8,
"diskNameFilter": {
"operator": "STARTS_WITH",
"value": "C"
},
"tagFilters": []
}
Response body
{
"id": "fdd83212-9c08-44ba-a0cf-dbb471cd819a",
"name": "very slow disk"
}
Response code
204
Result
The new rule looks like this in the UI: