Request attributes
DESK tracks all requests, from end-to-end, and automatically monitors the services that underlie each transaction. The performance and attributes of each request can be analyzed in detail. You can even create custom multi-faceted filters that enable you to analyze call sequences from multiple perspectives. With such advanced request filtering, DESK enables you to slice and dice your way through your requests to find the proverbial “needle in the haystack.” Such filtering isn't only possible on certain predefined attributes. You can also configure custom request attributes that you can use to improve filtering and analysis of problematic web requests.
How to make use of request attributes
Once you've defined your request attributes, you can use them to:
- Filter your monitoring data
- Define web-request naming rules
- Set up detection of business-logic related errors
- Build your own custom analysis charts
- Enrich PurePath analysis by adding metadata to PurePaths
- Create custom metrics using the Timeseries API
- Create custom queries, segmentation, and aggregation of session data with User Session Query Language
- Other ad hoc analysis
Understand request attributes
Request attributes are essentially key/value pairs that are associated with a particular service request. For example, if you have a travel website that tracks the destinations of each of your customers’ bookings, you can set up a destination attribute for each service request. The specific value of the destination attribute of each request is populated for you automatically on all calls that include a destination attribute (see the easyTravel destination attribute example below).
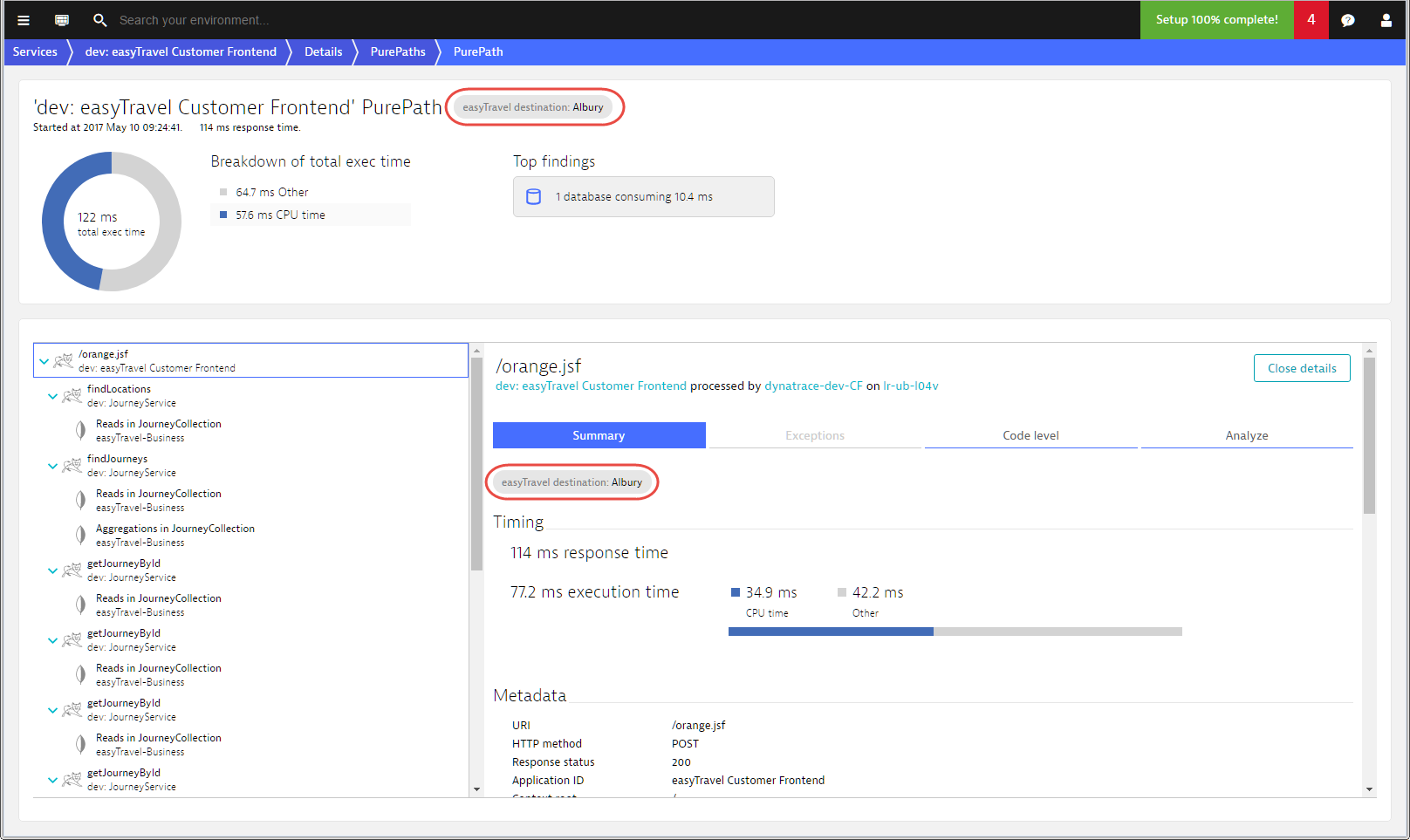
If an attribute exists on multiple requests within a single PurePath, then the attribute is applied to each request. In such instances, a single attribute may have varying values for each transaction request in the PurePath. You can even have multiple attributes on the service calls within a single PurePath. This makes request attributes a powerful and versatile feature when combined with DESK advanced filtering.
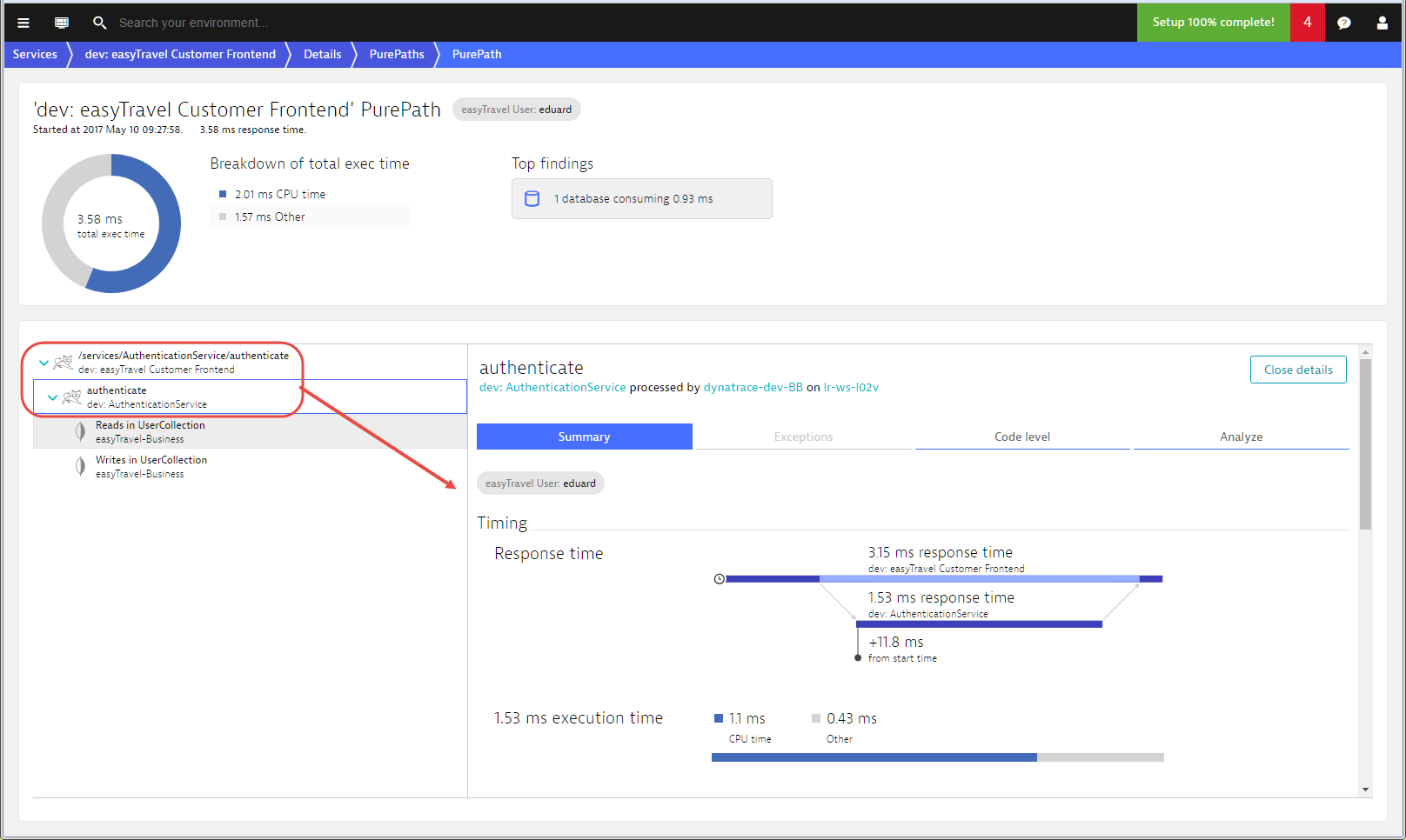
In the image below you can see that the easyTravel User attribute exists on the triggering request (/services/AuthenticationService/authenticate) as well as on the authenticate request of the AuthenticationService that is called.
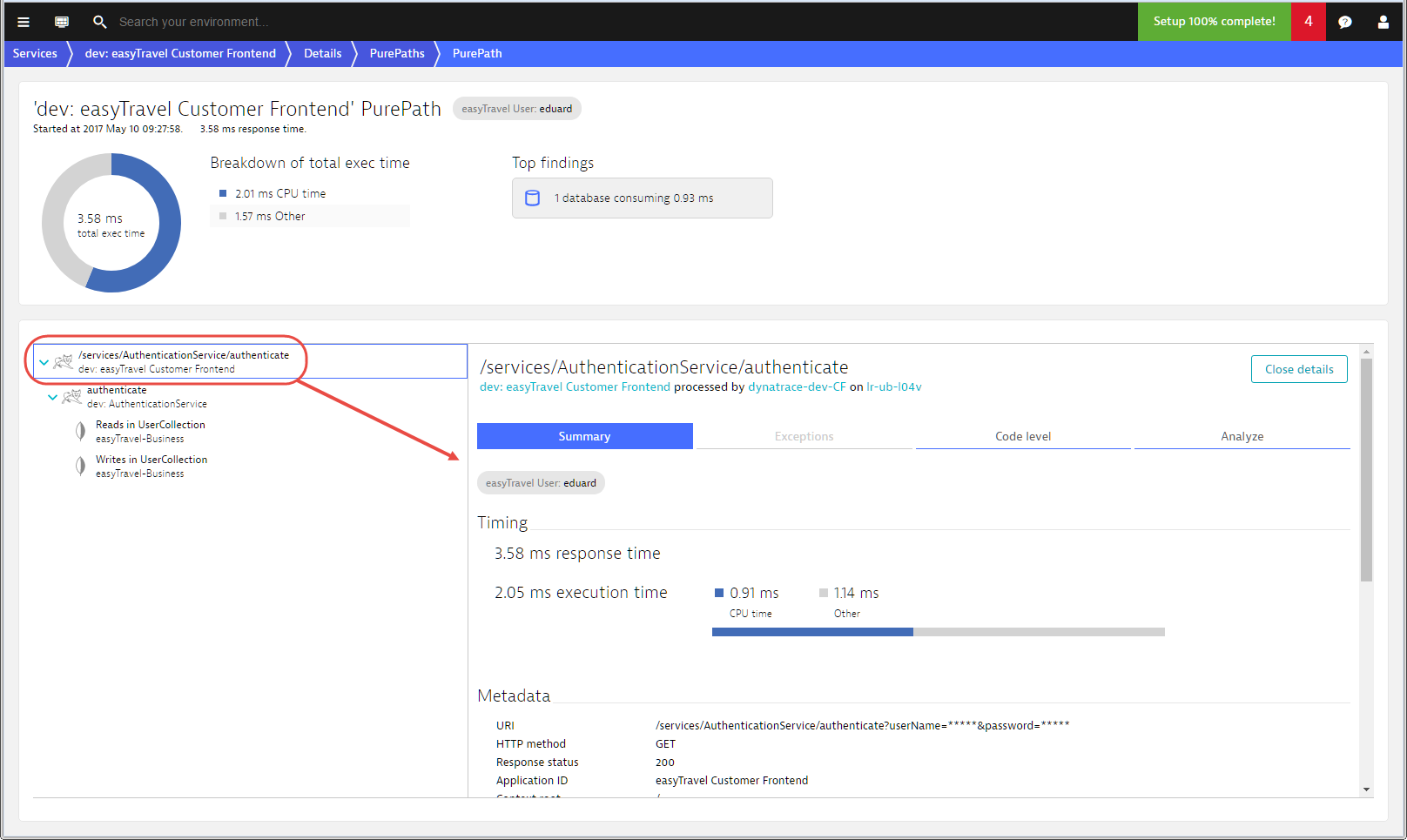
In this example, the value is the same, however your application may be different and the values may therefore not be identical.
Define request attributes
Request attributes can be defined based on:
- web request data
- Java method arguments
- .NET method arguments
- any data captured with the OneAgent SDK
Mark request attributes as confidential
As request attributes may include confidential values, DESK makes it possible to mark a request attribute as confidential. To do this
- Go to Settings > Server-side service monitoring > Request attributes.
- Click the Edit button of the relevant request attribute.
- Select the Request attribute contains confidential data option box.
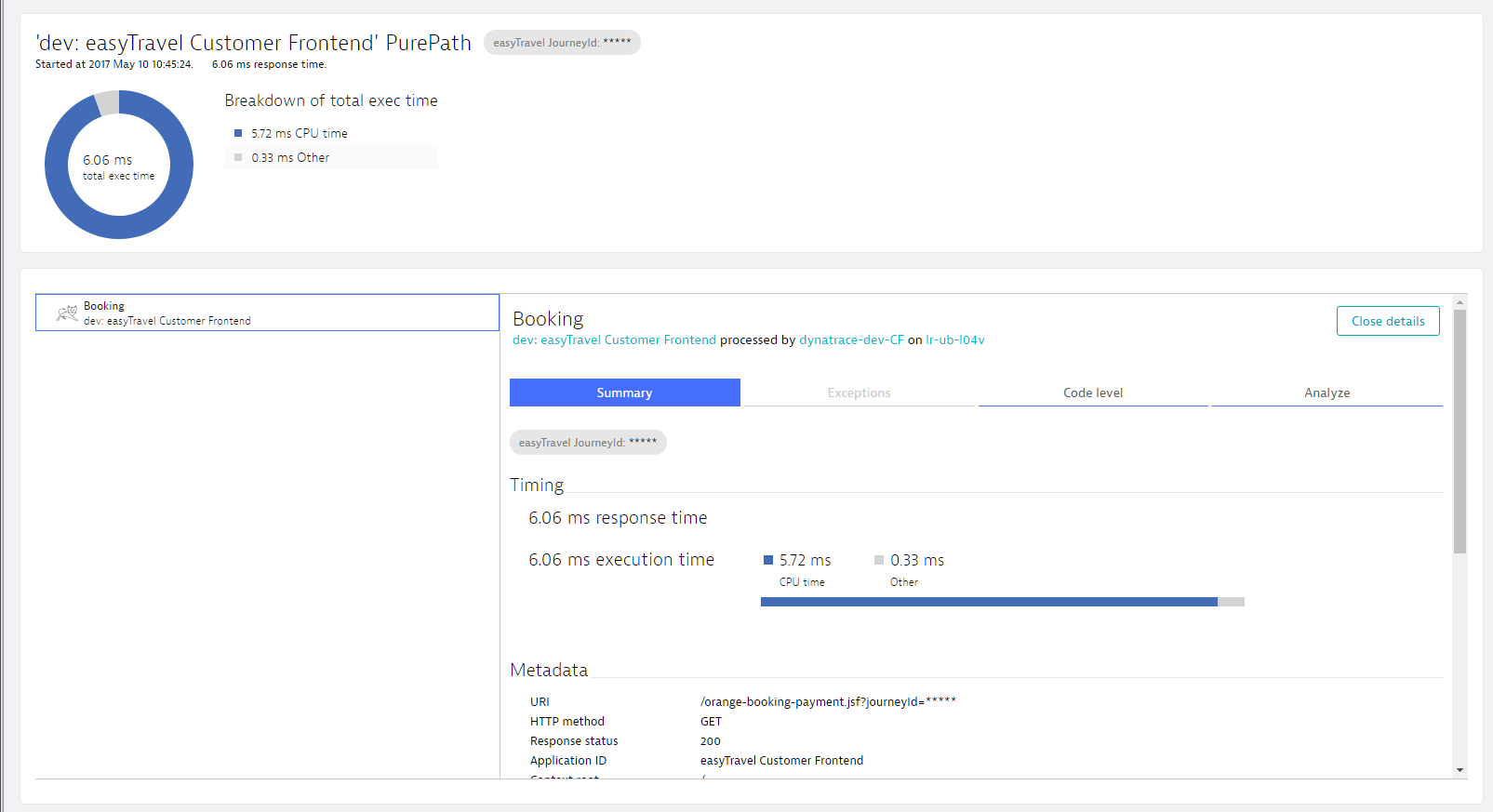
With this setting enabled, unauthorized DESK users see only an obscured view of masked data. For example, while unauthorized users can see all performance metrics related to the execution of a certain SQL statement, all sensitive values in the statement are represented with five asterisks (*****), and so are hidden from unauthorized access (see image below).
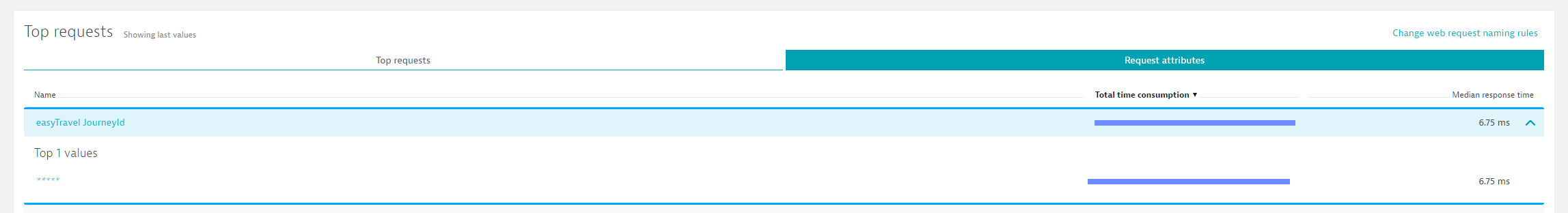
Looking at the PurePath, you can see that the actual JourneyId is hidden because this user doesn’t have permission to view confidential data.